Internet of Things
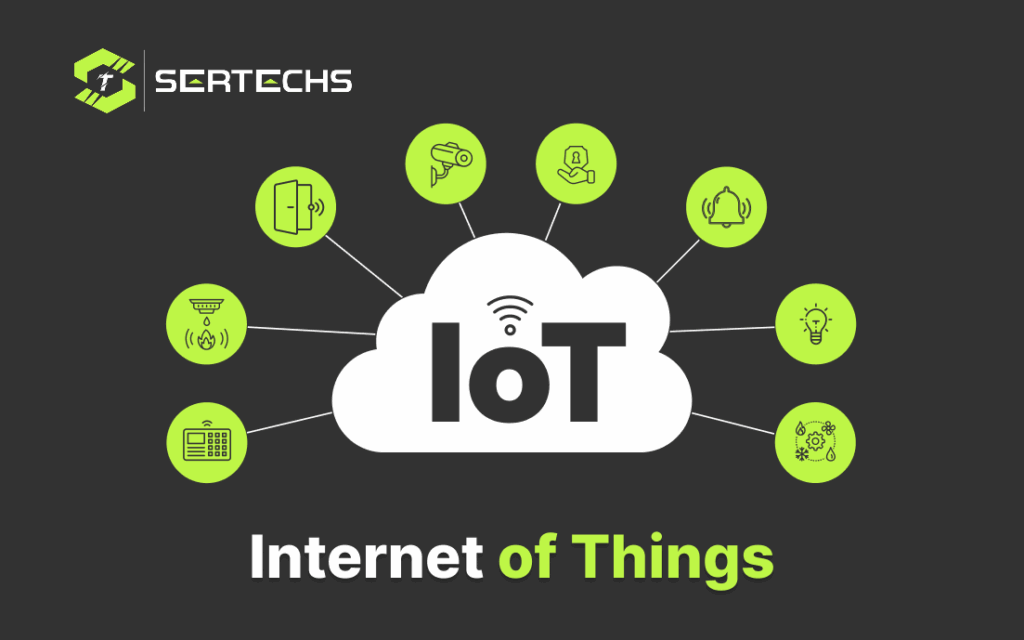
The Internet of Things (IoT) refers to a network of interconnected devices and systems that communicate and share data over the internet. These devices, often embedded with sensors, actuators, and connectivity capabilities, can collect, transmit, and receive data, enabling them to interact with their environment and other connected devices. Here are key aspects of IoT: Interconnected Devices: IoT encompasses a vast array of devices, including sensors, appliances, vehicles, wearables, industrial machines, and more. These devices can communicate with each other and with centralized systems. Sensors and Data Collection: IoT devices are equipped with sensors that collect various types of data such as temperature, humidity, light, motion, location, and more. This data is then transmitted for analysis and actionable insights. Connectivity: IoT devices use different communication protocols (e.g., Wi-Fi, Bluetooth, Zigbee, LoRa, cellular) to connect to the internet and share data. The choice of connectivity depends on the specific use case and requirements. Data Processing and Analytics: The data collected by IoT devices is processed and analyzed to extract meaningful insights. Advanced analytics, machine learning, and AI algorithms are often employed to derive actionable intelligence from the vast amounts of IoT-generated data. Automation and Control: IoT allows for automation and remote control of devices based on data analysis and predefined rules. For instance, smart thermostats can adjust heating or cooling based on occupancy and temperature patterns. Integration with Applications: IoT data and insights can be integrated into various applications, such as mobile apps or web interfaces, providing real-time monitoring, alerts, and control to users. Security and Privacy: IoT security is a critical concern. Measures are taken to ensure the confidentiality, integrity, and availability of data. Security protocols and encryption are utilized to protect IoT devices and data from unauthorized access and cyber threats. Industry Applications: IoT has diverse applications across industries, including smart homes, healthcare (remote patient monitoring), agriculture (precision farming), transportation (smart cars), manufacturing (Industry 4.0), energy management, retail (inventory tracking), and more. Scalability and Flexibility: IoT solutions need to be scalable to accommodate a growing number of connected devices. Flexible architectures and cloud-based platforms are often used to handle large-scale IoT deployments. Environmental Impact: IoT can contribute to sustainability efforts by optimizing resource usage, reducing energy consumption, and minimizing waste through smarter systems and decision-making.
Predictive analysis
Predictive analysis for this situation would involve forecasting potential future events or outcomes based on the available data and the incident described. Here are some possible predictions and recommendations: Increased Security Measures: Implementing enhanced security measures, such as a robust firewall, regular security audits, and continuous monitoring, will likely be a priority. Predictive analysis will help in proactively identifying and mitigating any potential security threats in the future. Regular Updates and Patching: A prediction would be that the website administrators will adopt a strict policy of regularly updating the WordPress core, themes, and plugins to ensure they are equipped with the latest security patches and features. This practice will significantly reduce the risk of future security breaches. Incident Response Plan: Establishing a comprehensive incident response plan to expedite the process of identifying, isolating, and resolving any security breaches. This plan would involve predefined steps to be followed in case of a similar incident, aiming to minimize damage and restore normalcy swiftly. Customer Trust Rebuilding: Recognizing the importance of rebuilding trust with customers after a security incident, strategies may include issuing public apologies, offering discounts or special offers, and showcasing the improved security measures to assure users of a safer browsing experience. Continuous Monitoring and Analysis: Anticipating the implementation of tools and techniques for continuous monitoring of website traffic, user interactions, and potential security threats. This will facilitate real-time analysis and early detection of suspicious activities, allowing for a prompt response. Legal and Compliance Considerations: Expecting a thorough review of legal and compliance requirements related to data protection and website security. Ensuring full compliance with relevant regulations will be crucial to avoid potential legal consequences and protect user data. In conclusion, the incident will likely serve as a catalyst for significant improvements in the website’s security posture, user education, incident response mechanisms, and overall user experience. The goal will be to transform this unfortunate event into an opportunity to enhance the website’s security and regain user trust.
Human-centric AI

Human-centric AI, also known as HCAI, refers to the design, development, and deployment of artificial intelligence systems and technologies with a primary focus on serving and benefiting humans. AI learns from human input and collaboration, focusing on algorithms that exist among a larger, human-based system. The following key principles of Human-centric AI: User-Centered Design: Human-centric AI starts with a deep understanding of the needs, preferences, and limitations of the end-users. AI systems are designed and developed with the user in mind, ensuring that they are intuitive, accessible, and user-friendly. Ethical Considerations of Human-centric AI: Ethical considerations are at the forefront of human-centric AI. Developers and researchers strive to create AI systems that respect human rights, privacy, and dignity. This includes addressing bias, discrimination, and other ethical challenges associated with AI. Transparency and Explainability: HCAI advocates for transparency in AI systems. Users should be able to understand how AI systems make decisions and have access to information about the data and algorithms used. Explainability is crucial, especially in critical applications like healthcare and finance. Collaboration with Humans: Rather than replacing humans, human-centric AI aims to augment human capabilities and collaborate with them. AI systems are designed to assist, empower, and enhance human decision-making and productivity. Privacy and Data Security: HCAI places a strong emphasis on protecting user privacy and ensuring the security of personal data. Adequate safeguards are put in place to prevent unauthorized access and data breaches. Accountability and Governance: There is a need for clear accountability and governance structures in HCAI. This includes establishing guidelines, regulations, and oversight mechanisms to ensure responsible AI development and deployment. HCAI is a holistic approach to AI development that prioritizes the well-being and interests of individuals and society as a whole. It seeks to harness the power of AI to improve human lives while minimizing potential risks and negative consequences.
Space Exploration
Space exploration refers to the human endeavor to explore and investigate outer space, including celestial bodies such as planets, moons, asteroids. It encompasses both crewed missions involving astronauts and robotic missions conducted by spacecraft and rovers. Space exploration serves several purposes and has numerous scientific, technological, and societal implications. The space age began with the launch of the Soviet satellite Sputnik 1 in 1957 and the subsequent manned spaceflight by Yuri Gagarin in 1961. The United States’ Apollo program culminated in the first human moon landing in 1969 by Neil Armstrong and Buzz Aldrin. Here are some key aspects of space exploration: Scientific Discovery: Space exploration allows scientists to study celestial objects and phenomena beyond Earth’s atmosphere. This research provides insights into the origins and evolution of our solar system, the universe, and the potential for extraterrestrial life. Human Spaceflight: Crewed missions, such as those conducted by NASA, ESA, Roscosmos, and other space agencies, have been sending astronauts into space. These missions contribute to our understanding of space, test new technologies, and offer valuable insights into the effects of long-duration. Robotic Exploration: Unmanned spacecraft and rovers, such as the Hubble Space Telescope, Voyager probes like Curiosity and Perseverance, allow scientists to explore distant celestial bodies. Space Telescopes: Space telescopes like the Hubble Space Telescope and the James Webb Space Telescope enable astronomers to observe distant galaxies and cosmic phenomena. Planetary Exploration: Planetary missions explore other celestial bodies within our solar system, including the Moon, Mars, Venus, and the outer planets. Space Science and Research: It contributes to various scientific disciplines, such as astrophysics, planetary science, astrobiology, and Earth sciences, by conducting experiments. Space Policy and International Relations: The governance and regulation of space activities, including space debris management, space traffic control are crucial aspects of space exploration. Space exploration continues to evolve, with ambitious goals such as returning humans to the Moon, sending astronauts to Mars, and exploring the outer reaches of our solar system and beyond.
What is Snowflake?

Snowflake is a cloud-based data warehousing platform that allows organizations to store, manage, and analyze large volumes of data in a scalable and efficient manner. It is designed to handle both structured and semi-structured data, making it suitable for modern data analytics and business intelligence needs. Here are some key features and aspects of Snowflake: Cloud-Native: Snowflake is built to leverage the power and scalability of cloud computing platforms like Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP). It offers the advantages of elasticity, scalability, and pay-as-you-go pricing. Data Warehousing: Snowflake serves as a data warehousing solution, providing a centralized repository for storing and managing data from various sources. Users can load data into Snowflake, create data models, and run SQL queries for analysis. Data Sharing: Snowflake enables secure data sharing between organizations, departments, or partners without the need to copy or move data. This is particularly useful for collaborative analytics and sharing insights. Multi-Cluster, Shared Data Architecture: Snowflake employs a unique architecture that separates storage and compute resources. This allows for independently scaling compute clusters to handle different workloads while sharing a common data repository. Concurrency: Snowflake supports high levels of concurrency, allowing multiple users to run queries simultaneously without significant performance degradation. This is crucial for large organizations with many users accessing the data warehouse. Security and Compliance: Snowflake prioritizes data security and compliance with features like encryption, role-based access control, auditing, and support for various industry-specific compliance standards. Seamless Integration: It integrates with various data integration and ETL (Extract, Transform, Load) tools, business intelligence platforms, and analytics frameworks, making it easier to work with existing data ecosystems. Data Sharing and Exchange: Organizations can share data with external partners and customers securely using Snowflake’s data sharing capabilities. This is beneficial for collaboration and monetizing data assets. Scalability: Snowflake can scale both vertically and horizontally to handle growing data workloads. Users can allocate more or fewer resources as needed, making it cost-effective. Performance Optimization: The platform includes features for query optimization and automatic scaling, ensuring that queries run efficiently and quickly, even on large datasets. Snowflake has gained popularity as a versatile and powerful data warehousing solution for organizations looking to harness the full potential of their data. Its cloud-native architecture and flexibility make it a valuable tool for data analytics, data engineering, and business intelligence in various industries.
Extended Reality

Extended Reality is an umbrella term that encompasses various immersive technologies, including Virtual Reality, Augmented Reality, and Mixed Reality. XR blends the physical and digital worlds to create interactive and immersive experiences for users. Here’s an overview of these different components of XR: Virtual Reality (VR): Virtual Reality is a technology that immerses users in a completely virtual, computer-generated. Users typically wear VR headsets that cover their field of vision and often include sensors. Augmented Reality (AR): Augmented Reality overlays digital content, such as images, videos, or 3D models, onto the real world. AR applications are usually experienced through mobile devices like smartphones or tablets, but AR glasses are becoming more common. Mixed Reality (MR): Mixed Reality combines elements of both AR and VR to create an environment. Microsoft’s HoloLens is an example of an MR headset. Key aspects and applications of XR: Immersive Experiences: Extended Reality technologies provide users with immersive, interactive experiences that can be used for entertainment, education, training, and simulation. Training and Simulation: Extended Reality is valuable for training scenarios, such as flight simulators for pilots, medical simulations for healthcare professionals, and military training. Gaming: Virtual Reality is especially popular in the gaming industry, where it offers gamers highly immersive and lifelike experiences. Healthcare: Extended Reality is used in medical training, patient education, and even remote surgeries where a surgeon can use XR to visualize and manipulate digital data. Architecture and Design: Extended Reality is used for architectural visualization, allowing architects and clients to explore building designs in a virtual environment. Remote Collaboration: Extended Reality can enable remote teams to collaborate in shared virtual spaces, making it easier for professionals from different locations to work together. Retail and Marketing: Augmented Reality is used in retail apps to allow customers to visualize products in their real environment before making a purchase decision. Extended Reality continues to evolve with advancements in hardware and software, and it has the potential to transform industries and interact with digital content and the physical world.
Cloud Native Technologies

Cloud Native Technologies refers to a set of practices and methodologies that leverage the capabilities of cloud computing to build and run applications. Cloud-native applications are designed to fully utilize the advantages of cloud platforms, such as scalability, elasticity, and high availability. This approach is distinct from traditional software development and deployment methods. The focus is on building, deploying, and managing applications in a way that leverages the scalability, flexibility, and resilience provided by cloud environments. Key characteristics of Cloud Native Technologies include: Microservices: Cloud-native applications are typically built as a collection of loosely coupled microservices. Each microservice is a self-contained unit responsible for a specific function, allowing for easier development, deployment, and scaling. Containerization: Containers, such as those managed by Docker, are a fundamental part of cloud-native technology. Containers package an application and its dependencies into a standardized unit, ensuring consistency and portability across different environments. DevOps Practices: Cloud-native development embraces DevOps principles, fostering collaboration between development and operations teams. Continuous integration and continuous delivery (CI/CD) pipelines are commonly used to automate software development, testing, and deployment processes. Scalability and Elasticity: Cloud-native applications are designed to scale horizontally, meaning they can handle increased traffic or workloads by adding more instances of microservices. They can also automatically scale down during periods of low demand to optimize resource usage and costs. Security: Security is a critical concern in cloud-native technology. Best practices include identity and access management (IAM), encryption, and security scanning of container images to identify vulnerabilities. Serverless Computing: Serverless computing allows developers to run code without managing the underlying infrastructure. While not strictly required for cloud-native applications, it’s often used for specific functions or tasks within a broader application. Cloud-native technology enables organizations to build and operate applications that are agile, scalable, and resilient in cloud environments. It has become increasingly popular as more businesses migrate to the cloud and seek to take full advantage of cloud-based resources and services.
What is Cybersecurity?
Cybersecurity refers to the practice of protecting computer systems, networks, devices, and data from theft, damage, unauthorized access, or any other form of cyber threats or attacks. Its primary goal is to ensure the confidentiality, integrity, and availability of information and computing resources. It encompasses a wide range of practices, technologies, processes, and measures designed to safeguard digital information and ensure the confidentiality, integrity, and availability of data. Key components of cybersecurity include: Information Security: Protecting sensitive data from unauthorized access, disclosure, alteration, or destruction. This involves encryption, access controls, and data loss prevention measures. Network Security: Securing the infrastructure that connects computers and devices, such as firewalls, intrusion detection systems, and virtual private networks (VPNs). Endpoint Security: Ensuring the security of individual devices, such as computers, smartphones, and tablets, through antivirus software, anti-malware tools, and security patches. Application Security: Protecting software and applications from vulnerabilities and threats by using secure coding practices, penetration testing, and regular updates. Cloud Security: Safeguarding data and applications stored in cloud environments through authentication, encryption, and access controls. Identity and Access Management (IAM): Managing and controlling user access to systems and data, including multi-factor authentication and role-based access control. Incident Response: Developing plans and procedures to address and mitigate cybersecurity incidents when they occur, including identifying, containing, and recovering from breaches. Security Awareness and Training: Educating employees and users about cybersecurity best practices to reduce the risk of human errors that can lead to security breaches. Security Policies and Compliance: Establishing policies, standards, and procedures that comply with relevant regulations and industry best practices. Cybersecurity is critical in today’s digital age because cyber threats are constantly evolving and becoming more sophisticated. Organizations and individuals need to continuously adapt their security measures to protect against a wide range of threats, including malware, phishing attacks, ransomware, data breaches, and more. Failure to implement robust cybersecurity measures can result in financial losses, reputational damage, and legal consequences.
Augmented Reality and Virtual Reality

Augmented Reality and Virtual Reality are two immersive technologies that alter our perception of the physical and digital worlds. AR blends digital content with the real world. It overlays computer-generated images, sounds, or information onto the user’s view of the physical environment, enhancing their perception of reality. VR creates a completely immersive digital environment that isolates users from the physical world. It often involves wearing a VR headset that covers the user’s field of view with a computer-generated 3D environment. Augmented Reality (AR): Augmented Reality (AR) is a technology that enhances a person’s perception of the real world by overlaying computer-generated information, such as images, videos, sounds, or 3D models, onto their view of the physical environment. AR blends the digital and physical worlds, allowing users to interact with both simultaneously. Devices: AR experiences can be accessed through smartphones, tablets, smart glasses, and heads-up displays (HUDs). Popular examples include the Pokémon GO game and Snapchat filters. Applications: Navigation and wayfinding (AR navigation apps) Training and education (medical simulations) Marketing and advertising (interactive product catalogs) Gaming (AR gaming like Pokémon GO) Industrial and maintenance tasks (overlaying instructions on machinery) Virtual Reality (VR): Virtual Reality (VR) is a technology that immerses users in a computer-generated, three-dimensional environment, which can be entirely different from the real world. VR creates a sense of presence, making users feel like they are physically present in the virtual environment. Devices: VR requires specialized hardware, such as VR headsets (Oculus Rift, HTC Vive) and motion controllers. These devices track the user’s movements and enable them to interact with the virtual environment. Applications: Gaming (immersive VR games) Training and simulation (flight simulators) Healthcare (therapy and pain management) Architecture and design (virtual walkthroughs) Education (virtual field trips) Both AR and VR continue to evolve and find new applications in various industries. Mixed Reality (MR) is a term used to describe experiences that blend elements of both AR and VR, offering users the ability to interact with digital objects in a real-world context.
Relation of Robotics & Automation

Robotics and automation refer to the use of machines and computer systems to perform tasks with minimal human intervention. Relation of Robotics & Automation involves the design and creation of physical robots, while automation typically involves the use of software and technologies to control and streamline various processes, such as manufacturing, logistics, and data analysis. Both robotics and automation aim to improve efficiency, accuracy, and productivity in a wide range of industries. Robotics and automation have a wide range of applications across various industries, including: Manufacturing: Automation is extensively used in manufacturing to assemble products, perform quality control checks, and handle repetitive tasks. Industrial robots are employed for welding, painting, and material handling, improving efficiency and safety. Healthcare: Robotic surgery systems assist surgeons with precision and minimally invasive procedures, while robotic exoskeletons aid in rehabilitation. Robots are also used for drug discovery and laboratory automation. Agriculture: Agricultural robots perform tasks such as planting, harvesting, and monitoring crops. Drones equipped with cameras and sensors help with crop management and surveillance. Automotive: Robotic arms are used in car manufacturing for welding, painting, and assembly. Autonomous vehicles represent the future of transportation. Space Exploration: Robots and rovers are used for planetary exploration, performing tasks like collecting samples and conducting experiments in harsh environments. Entertainment: Robotics and automation are used in animatronics for theme parks and in the creation of special effects for movies and television. Defense and Security: Unmanned aerial vehicles (UAVs) and ground-based robots are used for surveillance, reconnaissance, and bomb disposal to protect military personnel and civilians. Food Industry: Automation is used in food processing and packaging, from sorting and washing produce to filling and sealing containers. Relation of Robotics & Automation are just a few examples, and the applications of robotics and automation continue to expand as technology advances. These technologies are often adopted to increase efficiency, reduce costs, improve safety, and perform tasks that are dangerous, repetitive, or require high precision.

